10 Most Vulnerable WordPress Plugins (Updated)
Bulletproof Backups for Your WordPress Website
Fortify your business continuity with foolproof WordPress backups. No data loss, no downtime — just secure, seamless operation.
In WordPress, popular plugins are often the most exploited plugins. There is a reason for that: the more popular a plugin is, the more sites it is installed on, and therefore the rewards of a vulnerability on a popular plugin are huge for a hacker.
In order to protect your website, it is important to be aware of vulnerable plugins in WordPress and the common vulnerabilities that may be present in them. Luckily, we have compiled an essential list of vulnerable WordPress plugins that covers all of this information for you.
TL;DR: If you use plugins on your WordPress website, you should know if they are making your website vulnerable to hacks. While any plugin can have vulnerabilities, it is important that you understand the nature of vulnerabilities and secure your website proactively with a security solution such as MalCare.
List of Popular Vulnerable WordPress Plugins
Here is a list of the 10 top vulnerable WordPress plugins that have either had vulnerabilities or often identify vulnerabilities and hacks due to being immensely popular. Developers usually patch these vulnerabilities immediately after they are identified, so if you happen to have these plugins, update them immediately.
Note: Vulnerabilities in plugins do not reflect upon the efficacy or reliability of the plugin itself. Some plugins like Contact Form 7 and NextGen Gallery keep getting hacked simply due to their popularity. Although, their teams are efficient and release patches as soon as a vulnerability is found.
(Each Vulnerable WordPress plugin in this list will cover the following aspects: What the plugin is about, Vulnerabilities found, Impact, Patched or not)
1. Yoast SEO
Over 5 million active installations

Designed for website optimization, this SEO plugin is wildly popular. It has won its popularity thanks to its ability to help sites rank higher in search engines. But that higher rank is unstable, as Yoast’s vulnerabilities can cause severe damage to the sites it is a part of.
The Yoast SEO plugin is vulnerable, like many other plugins, to cross-site scripting attacks, the most recent one being identified in August 2021. These XSS attacks can include anything from new admin account creation, web shell installation, arbitrary redirects, up to full site takeovers.
Thankfully, this vulnerability was patched in version 5.0.4, so updating this plugin is vital to improved security.
2. SEOPress
Over 100,000 active installations
SEOPress is a popular SEO plugin, used to help optimize SEO for the users’ websites. However, as recently as August 2021, WordFence published a blog that revealed an XSS vulnerability in the plugin. The XSS vulnerability was found to affect all the websites using it and could possibly lead to a full website takeover.
Fortunately, WordFence communicated this issue to SEOPress before publishing the details of the vulnerability. And SEOPress promptly released a patch for the same. The vulnerability affected versions 5.0.0 – 5.0.3, so make sure you are updated to version 5.0.4 if you use SEOPress.
3. WooCommerce
Over 5 million active installations

Powering over 40% of WordPress-based businesses, WooCommerce is one of the most popular plugins out there. Unfortunately, this makes it a massive target for hackers, who can have a lot to gain if they gain access to these websites.
WooCommerce is an open-source eCommerce solution, suitable for multiple types of businesses. As such, the plugin allows for a lot of customization and versatility with many built-in tools and integrations. Users can choose how they want to get paid, configure shipping options, have it handle sales tax, and more.
WooCommerce most commonly experiences the following attacks through its vulnerabilities – XSS, PHP Object Injection, File Deletion, and Arbitrary File Upload. The most recent one was in July 2021, which made sites using Woocommerce susceptible to SQL injection attacks.
By activating cross-site scripting attacks, hackers can gain full access to your web server. This has a number of unfortunate results, including, and up to, the full shutdown of your website. Other risks include seizing your customer accounts via crafted images, escalating privileges via injecting code, being able to delete the index.php file, and more.
These vulnerabilities have been patched by version 5.2.2. Any prior versions contain these vulnerabilities as well as others, and consequently, you should update your plug-ins to the latest versions as soon as possible.
4. W3 Total Cache
Over 1 million active installations

Another SEO plugin, W3 Total Cache is extremely popular with those who want to improve their user experience along with their SEO. According to the WP Scan vulnerability database, the W3 Total Cache is one of the 10 Vulnerable WordPress plugins that have reported the highest number of vulnerabilities.
Most recently, two vulnerabilities that were exposed in W3 Total Cache made the plugin susceptible to XSS and RCE attacks. The vulnerabilities have been identified and patched in June 2021, and version 2.5.1 and newer are safe for use. So make sure to update your plugin if you use W3 Total Cache.
5. Elementor
Over 5 million active installations
Elementor is one of the most popular builders on WordPress, and therefore a lucrative target for hackers. Given the ease of building a website with drag-and-drop features, Elementor is one of the most commonly used plugins on WordPress.
In March 2021, security researchers at WordFence found an XSS vulnerability in websites that are powered by Elementor. This vulnerability allows attackers to gain access and seize control of the website.
Elementor promptly released a patch for the vulnerability that affected over 7 million websites. If your website uses Elemetor, update it immediately to at least version 31.4.
6. WP Statistics
Over 600,000 active installations
WP Statistics is a tool that allows you to know your website statistics without having to share your user’s data with third parties. It offers a visual representation of data and statistics of your website so that it becomes easier for you to gain insights about your users.
In March 2021, a vulnerability that allowed any site visitor to extract data via SQL injections was exposed. The WP Statistics team quickly managed to patch the vulnerability and versions 13.0.8 or higher are patched and safe to use.
7. Ninja Forms
Over 1 million active installations
As the name suggests, Ninja Forms is built for websites that need fillable forms. This drag and drop website form builder is wildly popular, with millions of downloads and clients.
This form builder is available as a WordPress plugin, with many interesting features like drag and drop fields, multipage and conditional forms, customizable row and column layouts, and more.
Due to its popularity, this plugin is a frequent target of hacking attacks, making it important to keep it updated.
One major vulnerability that older versions of Ninja Forms have is the one that allows XSS attacks. Otherwise known as a cross-site scripting attack, this attack is particularly dangerous under Ninja Forms, as an attacker can steal admin-level access and even take over your website. By merely importing a form containing malicious JavaScript, and replacing an existing contact form with the previously mentioned version, hackers can gain high-level access.
In January 2021, four different vulnerabilities were discovered within the plugin. Thankfully, these vulnerabilities have been patched in version 3.4.34.1. All users of Ninja Forms have been advised to update their plugins immediately.
8. NextGen Gallery
Over 700,000 active installations
The NextGen Gallery plugin is known as the industry’s standard WordPress gallery plugin, and for good reason. The plugin is immensely popular among photography sites.
In December 2020, WordFence reported several critical vulnerabilities in the NextGen Gallery plugin which included Cross-Site Request Forgery (CSRF), Remote Code Execution(RCE), and XSS vulnerabilities.
Imagely, the company that runs the NextGen Gallery plugin immediately published a patch that took care of all of these vulnerabilities within a day and secured its users. If you use NextGen Gallery, be sure to update it to version 3.5.0.
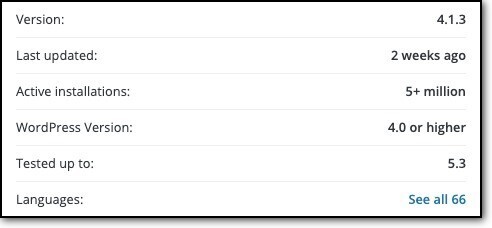
9. Contact Form 7
Over 5 million active installations
Contact Form 7 is one of the most widely used form plugins that is constantly targeted due to its popularity. With over 5 million users, it is a rather lucrative target for attackers. But the Contact Form 7 team is equally active when it comes to the security of the plugin. New patches are delivered swiftly as soon as vulnerabilities are identified.
Most recently, in December 2020, Contact Form 7 was found to have a privilege escalation vulnerability that was deemed critical by the WP Hacked blog. This vulnerability could be exploited to gain complete access to any website using the Contact Form 7 plugin.
The plugin team published a patch for the vulnerability right away, so if you are a user, make sure that you have version 5.3.2 or higher.
10. WordFence
Over 4 million active installations

Security plugins being vulnerable can be disheartening, but after all, they function on the same principle as the rest of the plugins. Security plugins, in fact, are often targeted by hackers in order to gain access to the websites that use them.
WordFence has over 4 million users and is one of the most popular security solutions for WordPress. But it has reported 11 vulnerabilities so far, the latest one reported in 2019, which was an XSS vulnerability.
WordFence promptly patched the vulnerability and it is not a threat to any website anymore. Just make sure that you are using the latest version of WordFence.
Common WordPress Plugin Vulnerabilities
Now that you know which common WordPress plugins have carried vulnerabilities, it is important to understand what vulnerabilities plague them. Understanding these vulnerabilities could help you understand the exact nature of the security concern and the risk associated with these Vulnerable WordPress plugins.
WordPress SQL Injections
SQL injections are one of the most common hacks that occur through vulnerabilities in plugins. This occurs when the plugin does not validate the information sent to the database through means like the forms on the website or the site search bar.
Hackers can exploit vulnerabilities by injecting malicious code through these inputs, and once the code is in your database, hackers can use it to create access for themselves or inject spam links.
Broken Authentication
Broken Authentication attacks are those which grant the admin access privileges to the attackers. These attacks take place through vulnerabilities that allow hackers to log in as the admin due to one of several reasons such as weak credentials or passwords, passwords shared over unencrypted networks, or Session IDs visible in the URL. Since hackers mimic the admin when exploiting these vulnerabilities, they can cause a lot of damage if they gain access.
Data Exposure
Data exposure attacks inadvertently expose the personal data of website users or sensitive business data which can cause a lot of damage. Data exposure is not the same as a data breach, although both are related. A hacker steals information in a data breach.
However, a data exposure attack takes place when stored data is not properly protected, which is a common vulnerability. The lack of security can be a result of weak or no encryption, flaws in the code, or mistaken uploads.
XML External Entity Issues
All websites contain a feature known as an XML parser. This particular bit of code is important for the running of websites, as it converts eXtensible Markup Language (XML) into readable code. However, not all parsers are built well, and some parsers have notable vulnerabilities.
These vulnerabilities can be taken advantage of by using what is known as an XML External Entity (XXE) attack. Ideally speaking, XML parsers receive XML, process it, and convert it into readable code.
But if a vulnerability is found, instead of merely converting the code, the parser returns extra data or executes malicious code. This can allow anything from data exfiltration and account access to DDoS attacks.
Broken Access Control
Broken access control attacks are also known as privilege escalation attacks because users can access parts of the website that they shouldn’t be able to when vulnerabilities are exploited for such an attack. For example, a contributor can access and edit the content on the website. These vulnerabilities generally occur due to oversight when writing code.
For example, a user may not be able to access admin privileges from their login page but if they use a higher privilege URL directly, they can access these privileges. This can allow attackers to steal information or gain unauthorized access to sensitive information.
Security Misconfigurations
This type of vulnerability arises when security configurations for your website are either left on default, not optimized, or misconfigured. This could leave big gaps in your website security and open your website to attacks. These vulnerabilities are configuration weaknesses that can either be present in the code or the subsystems of the plugins.
Cross-site Scripting
Cross-site scripting or XSS attacks are usually exploited through vulnerabilities in any unprotected input field on the website. If a website accepts raw input from users and it is published without validating, attackers can use input fields such as message boards and forms as vehicles to launch an XSS attack, which can affect users who visit your website and infect their browsers. Sometimes XSS attacks can also lead to website defacement.
Arbitrary file viewing
Source files are an important part of your website. They carry sensitive data that should not be accessible to anyone but the admin. Usually, there are security measures in place that do not allow third-party viewing of source files. But if there are no such measures, hackers can easily view your source files such as the wp.config.php file and access your website. This can be disastrous for your website.
Best Safety practices against plugin vulnerabilities
It is best to use trusted plugins to avoid any security incidents. But even trusted plugins like the ones we discussed above carry vulnerabilities. So what can be done to ensure maximum security?
To begin with, always download plugins from the WordPress repository. When downloading, take a look at the number of downloads, its last update, and active installations. This will give you a general idea regarding the upkeep, maintenance, and overall credibility of the plugin. You can also take the following steps on your end to ensure that your website is safe.
Install a security plugin
A security plugin is one of the most important measures you can take to secure your website. A complete solution such as MalCare can detect any vulnerabilities on your website and alert you before there are any security incidents.
Additionally, your site will enjoy its powerful firewall which wards off most attacks and alerts you of any suspicious activity.
Update your plugins regularly
Most plugin developers are constantly trying to improve their products, and this includes correcting any security flaws such as vulnerabilities. As soon as a vulnerability is found, the team behind the plugin will generally release a patch to circumvent the issue. Therefore, it is important that you update your website and the extensions on it regularly.
Frequently backup your website
Sometimes the vulnerabilities in a plugin or theme can break your website. In order to secure your website data, it is important to frequently back up your website on a separate server from that of your website or web hosting provider.
A solution like Blogvault is ideal for this purpose, as Blogvault saves your backups on secure servers and keeps your website data safe from hacks and malware. Additionally, Blogvault also scans user’s websites for vulnerabilities and notifies you in advance so that these vulnerabilities do not affect you.
Avoid common passwords
Common passwords such as your birthdate, or dictionary words, or even your favorite movie can be easily deciphered by attackers. In order to avoid that, use strong passwords. If you worry about having to remember difficult passwords, you can use a password manager that will remember all the passwords for you.
Set up 2FA login
If your passwords or credentials are compromised, attackers can gain unrestricted access to your account. However, you can add an extra layer of security to your website by setting up two-factor authentication.
Once you set up two-factor authentication, anyone trying to log in will have to use the account credentials, as well as to authenticate their identity in order to gain access to your website.
Avoid nulled plugins and themes
Nulled themes and plugins are free for a reason. Most often, these nulled extensions have malicious code added to them which can compromise your website and make it vulnerable to attacks.
So in order to secure your website, always buy your themes and plugins from trusted sources and make sure that they are reliable.
Implement website hardening
Hardening your website is a term used for taking necessary steps to secure your WordPress website, which is recommended by WordPress. This includes disabling the file editor in themes and plugins, using strong credentials, resetting passwords for all users, and changing security keys and salts.
If this sounds too complex to follow, you can check out our guide on WordPress Hardening, which will explain every detail of the process. Alternatively, a security plugin like MalCare will conduct site hardening for your website automatically at the click of a button.
Final Thoughts
No software is 100% secure, and vulnerabilities are a common occurrence in plugins. So instead of being intimidated by vulnerabilities, taking adequate precautions and understanding how to secure your website can be a big step in the right direction.
In case you suspect a hack or a vulnerability on your website, we recommend installing MalCare which will scan your website thoroughly and alert you if your website has been hacked. You can then auto-clean your website with just a click of a button. A security plugin like MalCare can offer you peace of mind while actively protecting your website.
FAQs
What is a vulnerable WordPress plugin?
The oversights in the development of a plugin lead to weaknesses that can be exploited by hackers. These weaknesses are known as vulnerabilities. Any plugins which have such weaknesses that could pose a security threat to the user are known as vulnerable WordPress plugins.
Developers of reliable plugins often patch these vulnerabilities as soon as they are identified. Therefore, updating your plugins regularly is important.
Are plugins bad for WordPress?
Plugins are a great way to customize your WordPress website. They allow you to add features and make your website more interactive. So no, plugins are not bad for WordPress websites.
As with any other software, plugins are also prone to security gaps or weaknesses which are known as vulnerabilities. These vulnerabilities can cause security incidents if not handled in time. However, hardening your website, using a security plugin, and updating your website regularly can help you avoid most security threats.
Does WordPress have security issues?
Like any other CMS, WordPress is not 100% secure. And since WordPress is so popular, it attracts a lot of attention—good and bad. Hackers have more to gain by finding security flaws in WordPress.
However, WordPress also has a vibrant and thriving community that constantly works towards addressing security concerns. There are way more solutions that come with a WordPress site than issues. By the virtue of its popularity, WordPress also has solved many of the issues that other CMS still face.
What WordPress plugins are vulnerable?
Many WordPress plugins experience vulnerabilities. It is only when they are identified that their impact can be measured. Also, vulnerabilities are not static and as soon as they are identified, the developers try to patch them. This is why you should regularly update your themes and plugins.
How to Avoid Vulnerable WordPress Plugins?
There is no way to completely avoid vulnerable plugins in WordPress as even trustworthy and popular plugins like WooCommerce have had vulnerabilities. The best way to ensure that your plugin is safe is to use reliable plugins from the WordPress repository. Look for the downloads, active installations, updates, and reviews to get an overview of how the team maintains the plugin you’re planning to use.
Tags:
Share it:
You may also like

How to Limit Form Submissions with Droip in WordPress
Forms are an indispensable part of any website because of their versatility, letting you collect information for various purposes! However, people with ill intentions often attempt to exploit these forms…

How To Manage Multiple WordPress sites
Management tools help agencies become well-oiled machines. Each task is completed with the least amount of effort and highest rate of accuracy. For people managing multiple WordPress sites, the daily…

PHP 8.3 Support Added to Staging Feature
We’ve introduced PHP version 8.3 to our staging sites. Test out new features, code changes, and updates on the latest PHP version without affecting your live website. Update PHP confidently…
How do you update and backup your website?
Creating Backup and Updating website can be time consuming and error-prone. BlogVault will save you hours everyday while providing you complete peace of mind.

Updating Everything Manually?
But it’s too time consuming, complicated and stops you from achieving your full potential. You don’t want to put your business at risk with inefficient management.

Backup Your WordPress Site
Install the plugin on your website, let it sync and you’re done. Get automated, scheduled backups for your critical site data, and make sure your website never experiences downtime again.




