How to Scan WordPress Database For Malware & Fix Your Site?
Bulletproof Backups for Your WordPress Website
Fortify your business continuity with foolproof WordPress backups. No data loss, no downtime — just secure, seamless operation.

Did you notice something strange in your database lately? Did you see a number of unknown tables or did you notice an unknown URL in the options table?
These are classic signs of a hacked database.
The WordPress database stores information from your WordPress website. When your database is hacked, hackers can steal information, redirect your website to a different website, among other things.
But don’t worry, infected databases are a common issue that WordPress sites owners face. And there is a way to recover your hacked database. You will need to scan and clean your website immediately.
There are two ways of doing this. You can scan and clean your hacked database manually or by using a plugin.
To manually remove malware from WP database you need to have knowledge about the database. Even then, the process is time-consuming. Hence manual scan and cleanups are best suited for users with technical expertise.
For users without any technical expertise, using a security plugin is the best option.
In this article, we’ll take you through the steps of scanning WordPress database for malware using a plugin. In case, you still want to pursue the manual route, we’ve detailed that as well.
TL;DR
To fix your website, you need to scan your WordPress database with MalCare immediately. It’ll locate the malware within a few minutes and enable you to clean your database. The plugin will also help you take preventive measures to ensure that your website remains protected against future hack attempts.
[lwptoc skipHeadingLevel=”h3,h4,h5,h6″ skipHeadingText=”In Conclusion”]
What is the WordPress Database?
A database is a digital warehouse that stores data from your WordPress website. Every website regardless of which CMS they are built on has a database.
WordPress automatically creates a database when you are building a WordPress website. It uses a database management software called MySQL to create the database.
A MySQL database has two functions – storing data and retrieving data.
What this means is when you publish a post or a page, it is stored in the database. And when a visitor tries to access the post or page, WordPress retrieves it from the database to display it to the visitor.
Quick Note: Some of you are probably aware that WordPress files also store data from your website. That’s true. But WordPress files and databases collect different types of data. To understand this difference, we recommend reading Beginners Guide to the Structure of a WordPress Website.
WordPress database can be accessed the hosting account. Only the website owner has access to the database unless he/she shares the hosting account credentials with someone. But hackers have found other ways to access the database, mainly by exploiting security flaws in a website. In the next section, we’ll tell you how a database is hacked.
The WordPress database is a digital warehouse that stores, retrieves and displays all the data of your website. Click To TweetHow Can My WordPress Database be Hacked?
There are 2 primary ways in which hackers can gain access to your WordPress database. Those are:
1. Launching SQL Injection Attacks
2. Launching Brute Force Attacks
1. Launching SQL Injection Attacks
Most WordPress websites enable users to add comments or contact the site admins or owners. Areas, where a user can enter their own text, is called ‘input fields.’
When input fields are not configured correctly, it can be exploited by hackers. Instead of writing a comment, hackers can insert malicious code.
Comments submitted on your website are stored in the database. That’s how the malicious code finds it’s way into your database and opens doors for hackers to access your database.
One example that comes to mind is the SQL code injections in Booking Calendar WordPress Plugin. The vulnerability allowed an attacker to enter bad SQL commands which were passed to the database. This allowed the attacker to view data from the database.
2. Launching Brute Force Attacks
The WordPress database can be accessed by logging into your hosting account with your credentials.
Hackers can launch brute force attacks in which they try to guess the username and password of your account.
If you have easy-to-guess credentials such as admin (username) and password123 (password), chances are your account can be hacked easily. Once they gain access to your hosting account, they exploit your database.
If you suspect that your database is hacked, you need to take certain website security measures immediately. This includes scanning and cleaning your database which we’ll guide you through in the next section.
If your database is hacked, you need to take steps to clean it immediately. Use MalCare’s Instant Malware Removal to clean malware from your website. Click To TweetHow to Scan & Clean a WordPress Database for Malware?
There are two ways to scan and clean the database of a WordPress website. You can do it manually or by using a plugin. We’ll show you both the methods.
Scan & Clean WordPress Database Using a Plugin
Not every security plugin is capable of finding and removing malware in the database.
- It’s hard to find malware in the database. It could be hidden anywhere. Most security plugins only look into places where malware is generally found. This means malware hidden anywhere else goes undetected.
- Moreover, most security plugins follow the old-school signature or pattern matching methods to find malware in the database. But using this method, the WordPress malware scanner can only find known malware and not new or complex ones.
- Moreover, many security plugins for WordPress have a long turn-around time. It can take something between a few hours to a few days to clean your database. We know that when your website is hacked time of the essence. Delay in cleaning your website can snowball the situation. For instance, your hosting provider may suspend your site and Google may blacklist your site.
You will need a plugin that isn’t plagued by these issues. MalCare is one such security plugin.
Instead of relying on old-school methods like signature or pattern matching it checks the pattern and behavior of codes to identify whether the code is malicious or not. That’s how it finds new and complex malware.
Moreover, the plugin goes beyond the known places where malware is generally found. It looks into nook and corner and investigates suspicious behavior. If there is malware on your website, MalCare will find it.
In the next section, we’ll show you how to use MalCare Security Plugin.
Scan & Clean WordPress Database With MalCare Security Plugin
Follow our step-by-step guide to scan your WordPress site and clean it if the scanner finds any infection.
Step 1: Download and install MalCare Security. Add your site to the MalCare dashboard and the plugin will start to run a WordPress malware scan on your website immediately.
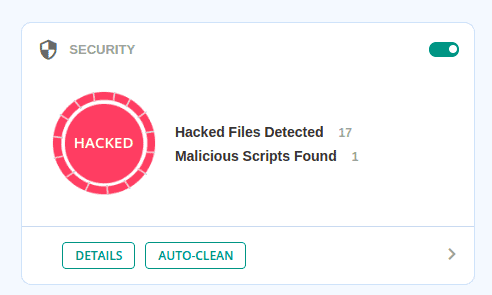
Step 2: After scanning your WordPress website, MalCare will inform you if it finds malware in your database.
Note that, the plugin scans both files and database, hence if it finds suspicious files, it’ll inform you about that too. On the website we scanned, MalCare found 17 WordPress hacked files and 1 malicious script in the database.
Step 3: If malware is present on your site, you need to get rid of it as soon as possible. With MalCare, you have an instant WordPress malware removal option. Just click on the Auto-Clean on MalCare’s dashboard and the plugin will begin cleaning your website.
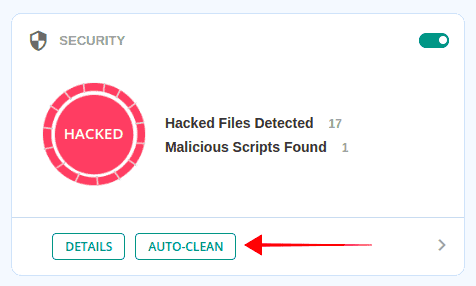
It’ll take a few minutes to clean your database but once complete, you will be notified about it in the MalCare dashboard.
Scan & Clean WordPress Database Manually
Manually scanning and cleaning the database is going to be time-consuming. Moreover, there is a good chance that you’ll miss hidden malware. Besides, if you make any mistakes while cleaning the database, such as deleting the wrong table or removing a piece of code that is not malicious, you may end up breaking your website.
This is why we strongly recommend scanning and cleaning your database with the help of a plugin. But if you are feeling adventurous today and want to try the manual method, go right ahead. But first, take a complete backup of your WordPress website. You can use a backup plugin like BlogVault to take a backup. In case something goes wrong, you can restore your backup and get your WordPress site up and running in no time.
In your database, there are two common indicators of malware. – Malicious PHP Functions and Unknown Links or iFrames. We will show how you can look for these manually.
- Malicious PHP Functions: One very common way of identifying infection in the database is the presence of potentially malicious codes like base64_decode, gzinflate, error_reporting(0), and shell_exec. That said, there is a drawback to this method. The codes are not always malicious. Sometimes programmers are known to use such code to execute certain functions.
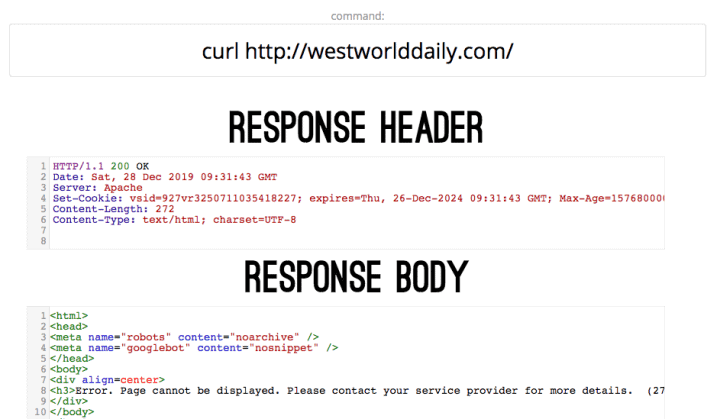
- Unknown Links or iFrames: Hackers insert unknown links and iFrames into the website and disguise it so that the site owner can’t identify the link. A good way of fishing out these links are examining your website code. You can use a tool named Online cURL to display and review the codes on your website. Carefully search for unwanted codes or suspicious texts like the name of pharmaceuticals drugs.
Once you’ve found signs of malware in your database, you need to clean it. To clean the database, you will have to restore a copy of the clean database. You can only do this if you have been taking WordPress database backups. But if you don’t have a clean backup to restore your website with, we suggest you use a backup plugin.
That’s it, folks. That’s the end of malware scanning and cleaning of your WordPress database.
if you want to export your WordPress database, we recommend you to go through our guide on how to export WordPress database?
In Conclusion
Getting your database hacked could be a wake call that you needed to take security more seriously. While your website may be out of danger now, there is no guarantee that it will never be hacked again. If you want to avoid such attacks from happening again, then it’s best to take certain WordPress security measures and use a security plugin and regularly scan WordPress database for malware. A plugin will offer you malware detection, cleaning, and measures to protect your website from future hack attempts.
Try out MalCare Security Plugin
Tags:
Share it:
You may also like

How to Limit Form Submissions with Droip in WordPress
Forms are an indispensable part of any website because of their versatility, letting you collect information for various purposes! However, people with ill intentions often attempt to exploit these forms…

How To Manage Multiple WordPress sites
Management tools help agencies become well-oiled machines. Each task is completed with the least amount of effort and highest rate of accuracy. For people managing multiple WordPress sites, the daily…

PHP 8.3 Support Added to Staging Feature
We’ve introduced PHP version 8.3 to our staging sites. Test out new features, code changes, and updates on the latest PHP version without affecting your live website. Update PHP confidently…
How do you update and backup your website?
Creating Backup and Updating website can be time consuming and error-prone. BlogVault will save you hours everyday while providing you complete peace of mind.

Updating Everything Manually?
But it’s too time consuming, complicated and stops you from achieving your full potential. You don’t want to put your business at risk with inefficient management.

Backup Your WordPress Site
Install the plugin on your website, let it sync and you’re done. Get automated, scheduled backups for your critical site data, and make sure your website never experiences downtime again.




