Common Attacks on WordPress Sites 101: Backdoors
Bulletproof Backups for Your WordPress Website
Fortify your business continuity with foolproof WordPress backups. No data loss, no downtime — just secure, seamless operation.
Removing malware from your website, and getting rid of hacks is a painstaking process. When you’re a website owner whose site has been hacked, your online reputation takes a hit. It’s only more distressing when you keep getting hacked. The reason behind this, most of the time, is a ‘backdoor’.
Having a backdoor could be explained with some ease, by comparing it to something we could call a “spare-key situation”.
Suppose you had a spare key to your house, but you dropped it somewhere on your street. Someone creepy has found it, and unfortunately for you, this person also knows exactly where you live. Of course, you don’t know about it, but you notice changes at home.
Whether all the furniture in your house is gone, or whether the sofa is always a little warmer in the morning depends entirely on what this person with the spare key is doing in your house. This means unless you change your locks or employ other security measures, this stranger has full access to your home and will keep coming back.
Hackers also do something similar when they hack WordPress sites.
When a hacker exploits a vulnerability and hacks a site, they want to be able to enter it again in the future. They also want to do so, without needing to put in the effort again. This becomes difficult though if the site owner closes the vulnerability by updating the exploitable theme/plugin. That is why hackers leave behind code called backdoors on the site. This way, even if the vulnerability is fixed, the backdoor remains. Backdoors are inconspicuous because the longer they stay hidden, the longer the attacker has a way to get back in.
Backdoors can give hackers complete control over Arbitrary Code Execution. One of the most common backdoors is ‘Filesman’. Since it’s feature-rich, it allows hackers to perform a variety of functions. However, there are others too, which might be just three-four words of code, but prove to be equally dangerous.
A lot of the time, backdoors are disguised as WordPress files and are hidden by the hacker in a place only they know. You, as an admin, could find the file only if you combed through all the WordPress files. This is especially difficult because backdoors can go in so many different places.
Here are a few places backdoors are usually hidden on your WordPress site:
- In core WordPress folders: Adding a new file to, or modifying an existing file in a core WordPress folder (e.g. wp-includes or wp-admin or wp-content) can easily go unnoticed. Especially in the wp-includes folder, since it contains every file ever included to the site. This is why we noticed a lot of backdoors here.
- In new, innocent-looking folders: Hackers could add hack files to new files that look completely innocuous, like ./images/
- Plugins and Themes: Not many people bother to check these folders after the plugins/themes have been installed. This makes these folders a perfect target. Moreover, a lot of plugins have their own vulnerabilities. Another way hackers install backdoors is by adding a new plugin to the site that looks normal but is actually malware.
Just to give you a general idea, this is how you identify a backdoor (that looks like a plugin file):
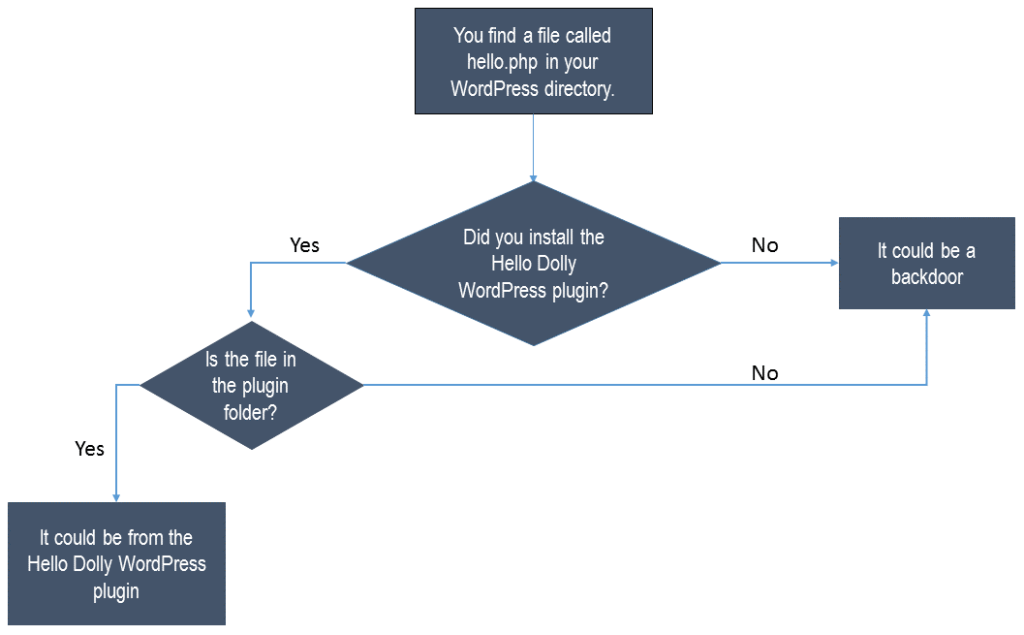
These vulnerabilities are sneaky. They can be passed off by a number of malware scanners as legitimate files, because of the way they’re named. This is why it’s so difficult to identify backdoors.
Backdoors are especially infuriating because sometimes hackers choose to leave more than one of them, in many locations. So even if one was discovered, there would be another way in.
Accurate, efficient scanning and hack removal requires time, and technical assistance (which is expensive usually). If you’d like to test the only one-click, automated hack-cleaner that misses nothing, and sounds no false alarms, we suggest that you try MalCare, for free.
Tags:
Share it:
You may also like

How to Limit Form Submissions with Droip in WordPress
Forms are an indispensable part of any website because of their versatility, letting you collect information for various purposes! However, people with ill intentions often attempt to exploit these forms…

How To Manage Multiple WordPress sites
Management tools help agencies become well-oiled machines. Each task is completed with the least amount of effort and highest rate of accuracy. For people managing multiple WordPress sites, the daily…

PHP 8.3 Support Added to Staging Feature
We’ve introduced PHP version 8.3 to our staging sites. Test out new features, code changes, and updates on the latest PHP version without affecting your live website. Update PHP confidently…
How do you update and backup your website?
Creating Backup and Updating website can be time consuming and error-prone. BlogVault will save you hours everyday while providing you complete peace of mind.

Updating Everything Manually?
But it’s too time consuming, complicated and stops you from achieving your full potential. You don’t want to put your business at risk with inefficient management.

Backup Your WordPress Site
Install the plugin on your website, let it sync and you’re done. Get automated, scheduled backups for your critical site data, and make sure your website never experiences downtime again.




