How to Fix “This Site Ahead Contains Harmful Programs” on WordPress?
Bulletproof Backups for Your WordPress Website
Fortify your business continuity with foolproof WordPress backups. No data loss, no downtime — just secure, seamless operation.
The warning “Site Ahead Contains Harmful Programs” can cause panic for any website owner! What does it mean? How is it going to impact your website and your business? Will you face serious consequences?
We are sorry to break this to you that the “Site Ahead Contains Harmful Programs” warning generally appears because the website is hacked. When search engines like Google and Mozilla Firefox detect malware on your site, they flag it as an unsafe site and display this warning to protect their users from accessing your website.
This can have a domino effect. If visitors are prevented from accessing your website, your traffic will decline. You’ll notice your rankings falling, and this will affect your revenue collection.
Added to all this, if your hosting provider finds out that your website is hacked, they’ll suspend your account until it’s fixed.
You can prevent all this from happening if you act fast and fix your hacked site and remove the warning.
In this guide, we’ll show you the exact steps that you need to take to help you fix “the site ahead contains harmful programs” warning. We will also tell you what measures you can take to ensure that the warning never appears on your website again.
TL;DR
If your WordPress site is hacked, you need to take measures to fix it fast. You can fix the hack on your site by installing MalCare. It will scan and clean your site and restore it to normal in under a few minutes.
[lwptoc skipHeadingLevel=”h1,h4,h5,h6″ skipHeadingText=”Final Thoughts”]
What Does “The Site Ahead Contains Harmful Programs” Warning Mean?
Search engines like Google prioritizes user experience and satisfaction. They ensure their users not only get the right answers to their search queries but that they are protected from any cyber threats. You can check our guide on website hack protection.
It’s risky for Google users to visit hacked websites because they could become targets of the hacker.
- Hackers could steal their data or redirect them to phishing sites.
- Hackers could trick them into downloading malware onto their devices.
- Visitors may be subjected to viewing inappropriate malicious content and ads.
This is only to name a few of the malicious acts hackers carry out.
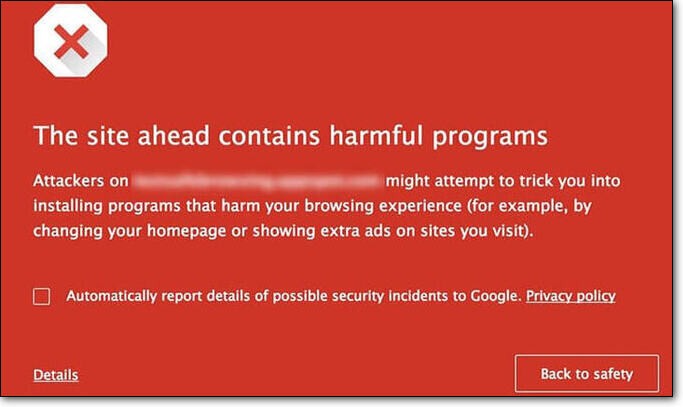
Thus, if your site is hacked, Google and other search engines, immediately flag your site and warn their users that your site isn’t secure. They display different warnings depending on why your site poses a risk. In case of malware, you will see the following or a similar red screen warning:
You may wonder how Google knows there’s malware on your site?
Search engines like Google constantly crawl the web for new sites and new content to index. They use bots and algorithms to check a website’s content is original and relevant. They can also check which websites are using deceitful tactics such as keyword stuffing.
During this process, they can also detect if there’s malicious code on your website. If they do, they proceed to:
- Blacklist your website immediately.
- Display “Site Ahead Contains Harmful Programs” or “This site contains malware” warnings to visitors.
- Depending on the risk posed by your site, it gives users an option to bypass their security warning and proceed to your site by clicking on ‘details’. Or they can choose to leave the site and go ‘back to safety’.
Now, you need to fix the hack as fast as possible to avoid hackers damaging your site and carrying out malicious acts. In the next section, we’ll show you the steps you need to take to remove the hack on your site.
How To Fix “Site Ahead Contains Harmful Programs” Warning?
To get the warning removed, you need to take the following five steps -:
- Scan and clean malware from your WordPress website
- Identify why your site was hacked
- Harden your WordPress Site
- Submit your site to Web Host (If your WordPress account is suspended)
- Submit your site to Google for review
Let’s begin.
1. Scan & Clean Malware From Your WordPress Website
In the first step, you need to scan your WordPress site and detect the malware. After that, you can proceed to clean it.
Now, both these steps can be carried out in two ways: manually or using a plugin. The manual method is a long one. It’s very technical in nature and above that, it’s not very effective when it comes to cleaning your site. This is because hackers cleverly disguise and hide their malware making it difficult to find manually.
The recommended way to scan and clean your site would be to use a WordPress security plugin. Here too, not all plugins are effective. We’ve seen many clients whose security plugin showed that their website was clean, but Google marked it as deceptive.
Note: Google will reject your review request if they find any trace of malware still present on your site. This is why we recommend using an automated tool like MalCare that’s designed to find any malware and get rid of it.
We recommend using our MalCare security plugin. Here’s why:
- The plugin is very easy to set up and use.
- It takes only a few minutes to detect WordPress malware on your site.
- Many plugins run only a surface scan that doesn’t check every file and folder of your site. MalCare analyses every inch of your site, including your database connection in WordPress.
- Some plugins rely on outdated technology of trying to locate malware and tend to miss any new malware hackers create. MalCare uses a method that will detect malware even if it’s new, disguised or hidden.
- MalCare is one of the only security plugins to scan your WordPress files as well as scan your WordPress database for malware. The plugin checks all elements of your site thoroughly.
- Most importantly, MalCare will get rid of any backdoors on your site. When a hacker breaks into your site, they usually create backdoors that give them secret access to your site. It’s extremely important that your plugin gets rid of these so that your site doesn’t get re-hacked.
Next, we can proceed to scan and clean up your WordPress website.
Step 1: Scan your WordPress site for malware
In order to clean your site, you need to identify where the malware is located and which files are infected. To do this, follow these steps:
- Install and activate MalCare on your WordPress site.
- Access MalCare from the left-hand menu on your WordPress admin dashboard.
- Here, enter your website name and select Malware Scan.
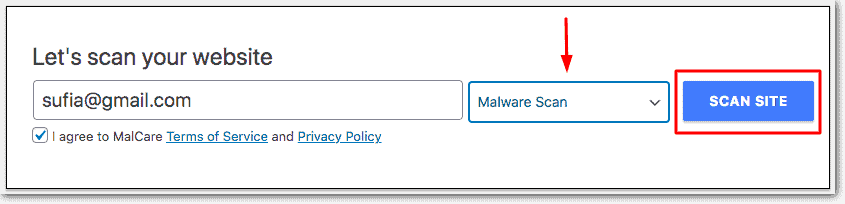
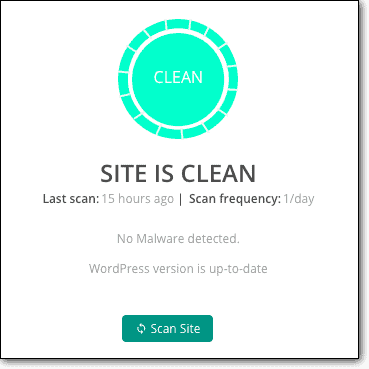
The plugin will redirect you to MalCare’s independent dashboard. Here, the automated malware scanning process will begin. It will identify all the malware present and show you how many files are infected:
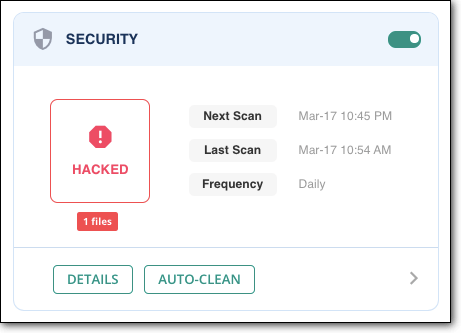
Step 2: Remove malware from your site
Once you’ve scanned your site, cleaning it with MalCare is even more simple.
- Under the number of hacked files, you’ll see a button called ‘auto-clean’. Simply click on that button and enter your FTP details.
- The plugin will clean your site automatically. Once it is done, it will show you that your website is clean. We suggest taking a screenshot of this page that indicates your site is clean. You’ll need it when you submit your site to Google for review.
Note: Malware removal is a complex process and is a premium feature in all security plugins. If you are a first-time user of MalCare, to use the auto-clean feature you would need to upgrade to a premium plan.
That’s it, your WordPress site is now clean. Next, you need to submit your site to Google for review. But Google’s safe browsing policies are very strict when it comes to malware on your site. So we advise you to take certain security measures on your site first. We discuss this in detail in the next section.
2. Identify Why Your Site Was Hacked
Imagine an intruder breaks into your home because the lock on your door was weak and easy to break. They ransacked your house and left. When you enter your home, you’re horrified. But you clean it up and put your house back in order.
Now, the next most important thing anyone would do is figure out how they broke into your home. In this case, you’d change the locks. This step makes sure the intruder won’t come back again.
The same applies to your website. It’s important to figure out how hackers broke into your site in the first place. We’ve listed out the top vulnerabilities that enabled hackers to break into your website.
i. Vulnerable themes and plugins
WordPress sites tend to have a multitude of themes and plugins installed. But did you know that it’s so common for themes and plugins to develop vulnerabilities over time? If a plugin or theme installed on your site is vulnerable, it makes your website vulnerable. That’s because vulnerabilities in plugins and themes can be exploited to gain access to your site. You can check some of the vulnerable WordPress plugins and themes here.
However, when vulnerabilities are discovered, developers quickly patch it and release an updated version of the software. Once you update to the new version, the vulnerability will be fixed on your site.
Now, many website owners delay updating their site either because updates come too often, or they experienced problems with updates. The reasons are plenty.
There are also times when website hackers find the vulnerability before the developers do. This enables hackers to exploit the vulnerability on your site and compromise it.
Make sure all your themes and plugins are updated. Delete any ones you don’t use or are inactive.
ii. Nulled or pirated themes and plugins
Nulled software gives you access to premium features for free and it’s tempting to use such versions. However, such software comes with preloaded malware. This enables hackers to gain access to any site that is using the infected plugin or theme. You can read here why you should avoid using nulled WordPress themes and plugins.
We don’t advise ever installing software and unwanted programs like this.
Delete all pirated versions of software, if any, and vow never to use them again.
iii. Visiting a malicious or phishing site
Hackers may trick you into opening a malicious link by sending you an email with a link or showing you an ad that seems genuine.
Upon clicking the link, you will be directed to a malicious website. These sites are coded in such a way that by simply visiting the site, it could infect your browser. Next, they use a technique called cookie stealing to find your login credentials and use it to break into your site.
Check your browser history to see if you visited any suspicious sites. We suggest clearing your browser’s cache and cookies.
iv. Infected Device Used to Manage the Website
We don’t see this happening too often, but it’s a possibility. If your computer or any device you’re using to access your website is infected, you risk infecting your site as well.
When hackers infect a computer, they inject their malware into several files. Now, if you upload one of those files to your website, the hacker can take advantage and compromise your site.
Use an antivirus program on your computer or device. Make sure your device is clean of any malware infection.
v. Weak login credentials
Hackers use a technique called brute-force to guess usernames and passwords of websites. They program bots to make thousands of login attempts in just a few seconds.
If you or any of your WordPress users have set login credentials like ‘admin’ and ‘password123’, it’s extremely easy for a hacker to guess it.
Make sure you inform every user of your website to use a strong username and password.
After identifying how hackers were able to break into your site, you need to take a few measures to ensure it doesn’t happen again.
3. Steps To Harden Your WordPress Site From Future Hack Attacks
There are certain measures WordPress recommends you take in order to strengthen your website. We strongly recommend implementing these hardening measures before proceeding with the site review.
(a) Change every user’s password
Ensure you use a strong password such as a passphrase combined with numbers and symbols. For example, weak password would be password123, but a strong password would be Thisisa$trongPassword123$
(b) Implement two-factor authentication
When using a two factor authentication a user has to enter their login credentials as well as a one-time password sent to their mobile or app. This verifies the user in real time.
(c) Install an SSL certificate
Data is constantly transferred from and to your site to servers and browsers. It’s important to protect this data from falling into the wrong hands. An SSL certificate will ensure that your data is encrypted and transmitted so no hacker can steal your data. You can get an SSL certificate from your host or from any SSL provider.
These measures are relatively simple to install. But there are also a few technical ones. They include:
- Disabling the file editor
- Disallowing plugin installation
- Changing WordPress security keys and salts
- Blocking PHP execution in certain folders
- Auto-logging out inactive users
You can implement these WordPress Hardening measures manually but it requires technical expertise. If you aren’t familiar with the inner workings of WordPress, we strongly recommend using MalCare to harden your site.
On the MalCare dashboard, access ‘Security’ by clicking on ‘Details’. Here, you’ll see an option to Harden your WordPress site.
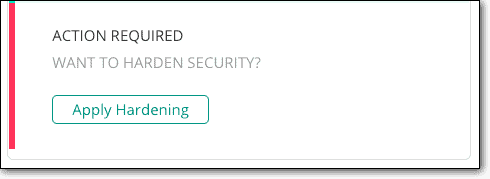
You can implement all these measures by simply clicking a few buttons. We strongly recommend reading our extensive Guide on WordPress Hardening.
Once you’ve hardened your site, we can proceed to submitting it to Google for review.
4. Submit Your Site To Web Host (If Account Is Suspended)
Web hosting providers also have ways to detect malware on your site. Once they do, they suspend your WordPress account and take your website offline. They do this to protect their platform and their servers.
If your WordPress hosting account is suspended, contact your web hosting provider and request them to remove the suspension. You can do this via phone, email or chat – depending on the customer support options your host provides.
Send them the details of your site along with the screenshot from MalCare that indicates your site is clean.
They will review your request, and upon finding your site clean, they will remove the suspension. The processing time depends on your host but it usually varies between 2-4 business days.
5. Submit Your Site For Review To Google
To remove the ‘site ahead contains harmful programs’ message, you have to submit your site for review.
But before you do so, you need to sign up or log in to Google Search Console. Verify ownership of your website. We’ve entailed the detailed process of verification in this article – Did Your Website Get Blacklisted by Google?
Once done, you can request a review to remove the Site Ahead Contains Harmful Programs warning in Google Chrome.
- Log in to Search Console and access Security Issues Report.
- Select ‘Request a Review’.
- Fill in the information required on what steps you took to remove the malware and secure your WordPress website.
- Submit your request.
Your review request will be processed between a day to several weeks. You will receive a response in your Messages in Search Console or Google Webmaster account.
Once Google determines that your website is clean, the warning will be removed within 72 hours.
Final Thoughts
To wrap up, we’d like to highlight two important measures we strongly recommend implementing on your WordPress blog site. These measures will make a difference in blocking hack attacks and recovering from it.
- Always keep a reliable WordPress security plugin such as MalCare active on your website. It will scan and check your site regularly and block hack attempts and malicious IP addresses with its WordPress firewall.
- Ensure you keep a working backup copy of your website. When things go wrong, you can restore your site to normal using your backup. If you’re using MalCare, backups are taken care of for you – powered by its sister plugin BlogVault.
You can have peace of mind knowing that you’ve taken the necessary security measures and precautions to keep your site safe.
Protect your WordPress Site from Hackers with MalCare!
Tags:
Share it:
You may also like

How to Limit Form Submissions with Droip in WordPress
Forms are an indispensable part of any website because of their versatility, letting you collect information for various purposes! However, people with ill intentions often attempt to exploit these forms…

How To Manage Multiple WordPress sites
Management tools help agencies become well-oiled machines. Each task is completed with the least amount of effort and highest rate of accuracy. For people managing multiple WordPress sites, the daily…

PHP 8.3 Support Added to Staging Feature
We’ve introduced PHP version 8.3 to our staging sites. Test out new features, code changes, and updates on the latest PHP version without affecting your live website. Update PHP confidently…
How do you update and backup your website?
Creating Backup and Updating website can be time consuming and error-prone. BlogVault will save you hours everyday while providing you complete peace of mind.

Updating Everything Manually?
But it’s too time consuming, complicated and stops you from achieving your full potential. You don’t want to put your business at risk with inefficient management.

Backup Your WordPress Site
Install the plugin on your website, let it sync and you’re done. Get automated, scheduled backups for your critical site data, and make sure your website never experiences downtime again.




